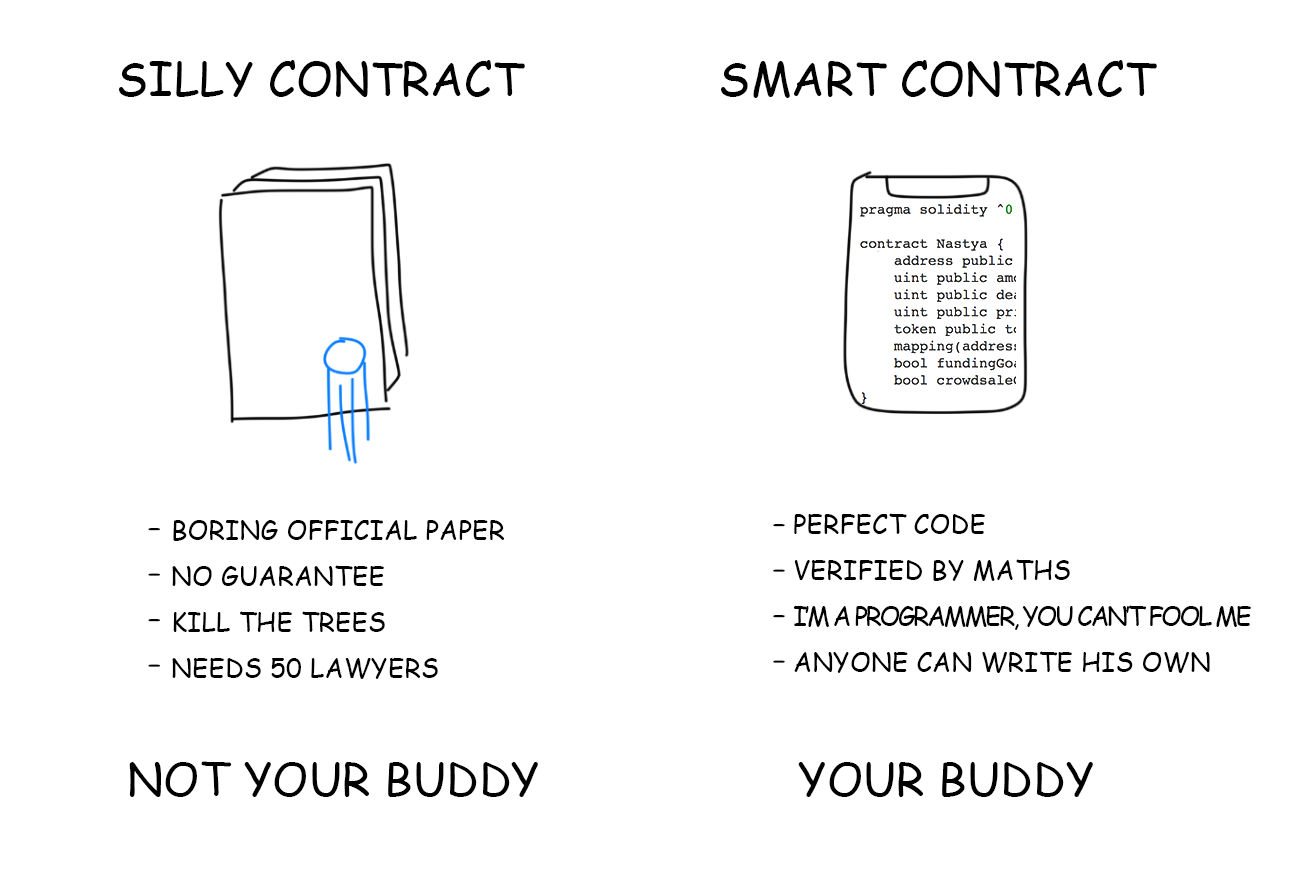
How Ethereum and Smart Contracts Work :: Distributed Turing Machine with Blockсhain Protection :: vas3k.com

DragonEX Incident Investigation Report: Tracking the Stolen $6M (USD) Asset Movements | by PeckShield | Medium

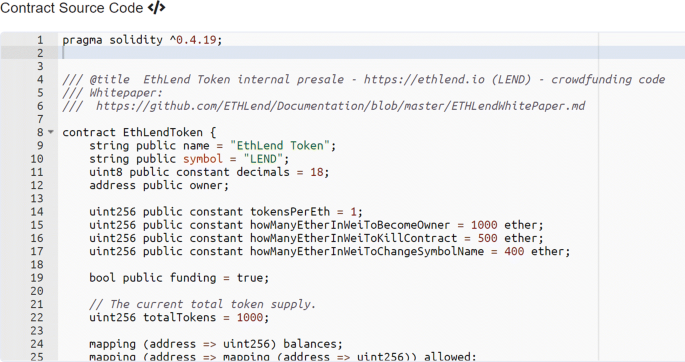
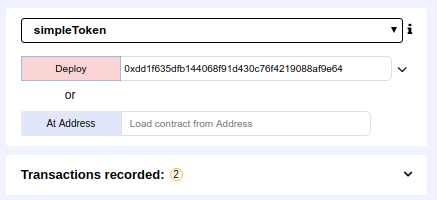
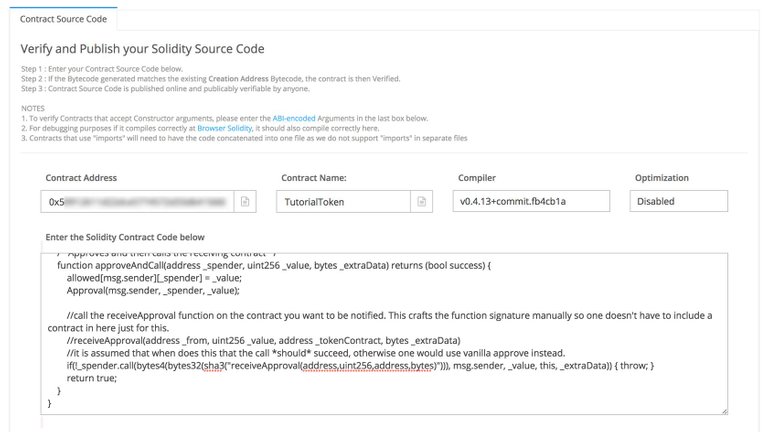
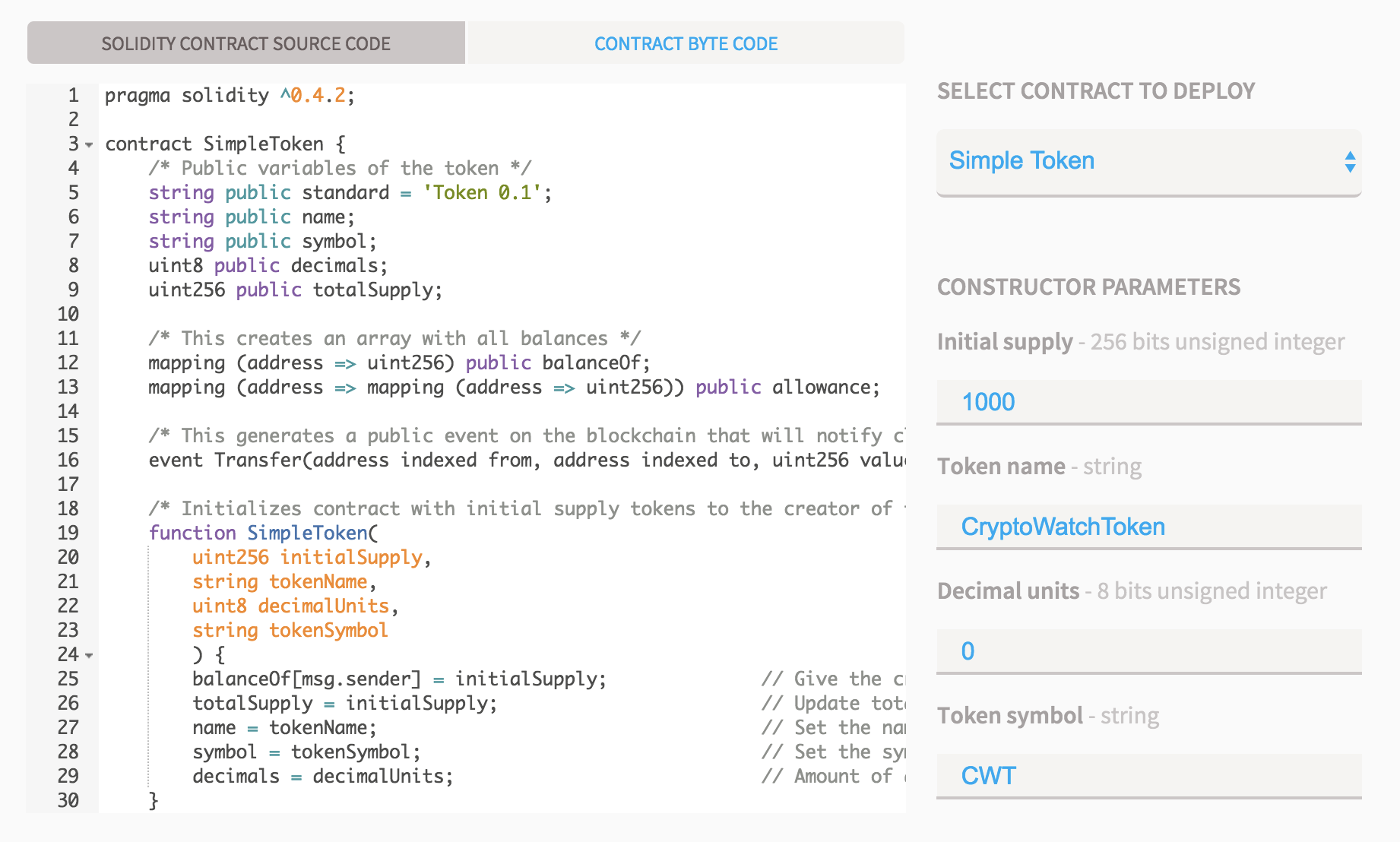
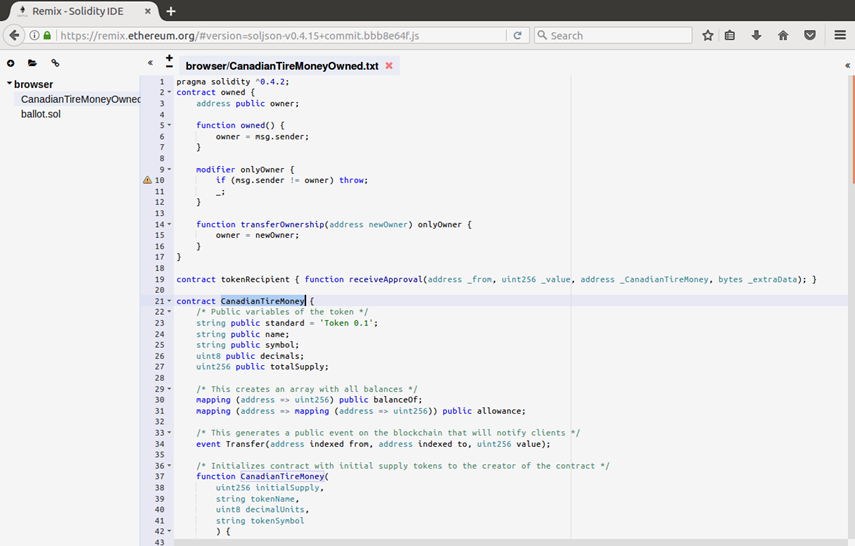
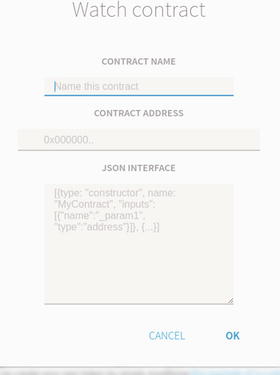
Create token contract and time-limited Crowdsale contract with whitelisting in solidity | by Tadej Oremuž | Coinmonks | Medium
Implementing Blockchain Technology in Irrigation Systems That Integrate Photovoltaic Energy Generation Systems

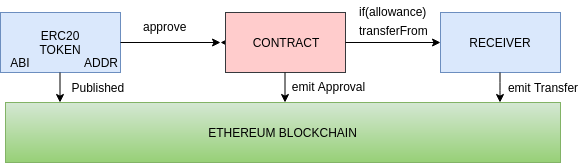
A Recipe for Creating Fully Decentralized Token Exchanges | by Dominic Williams | The Internet Computer Review | Medium

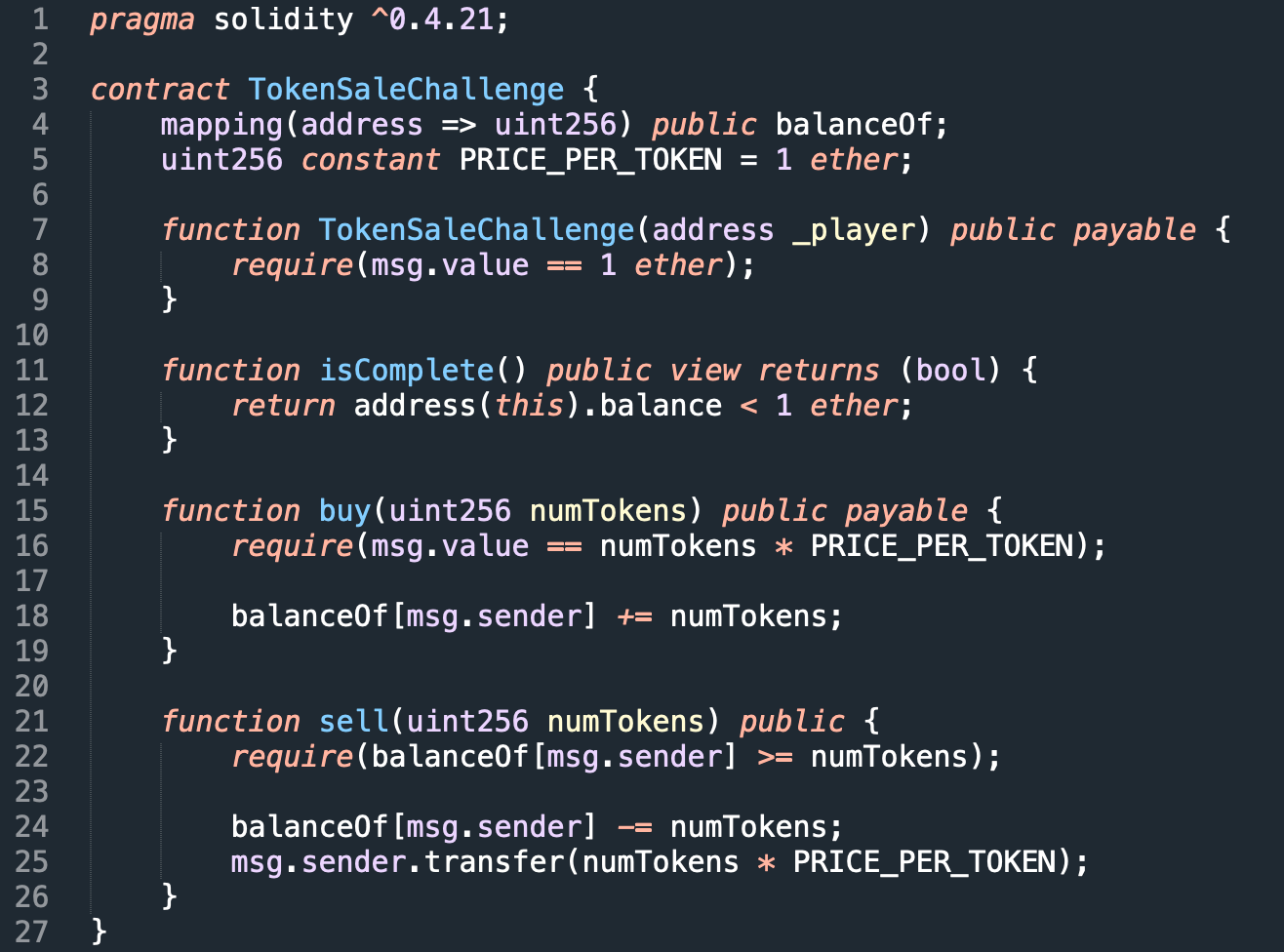
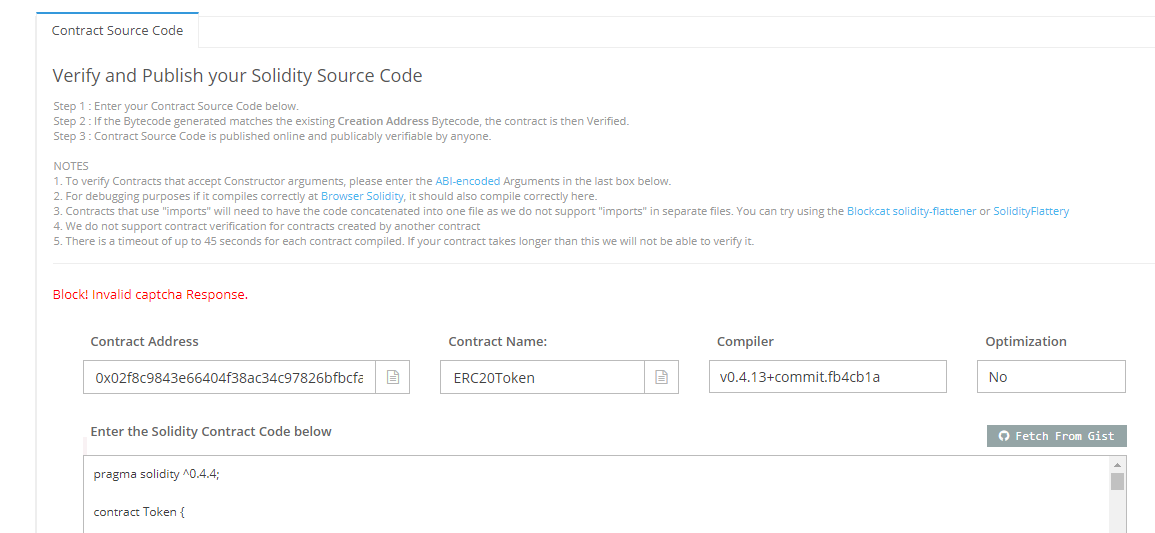
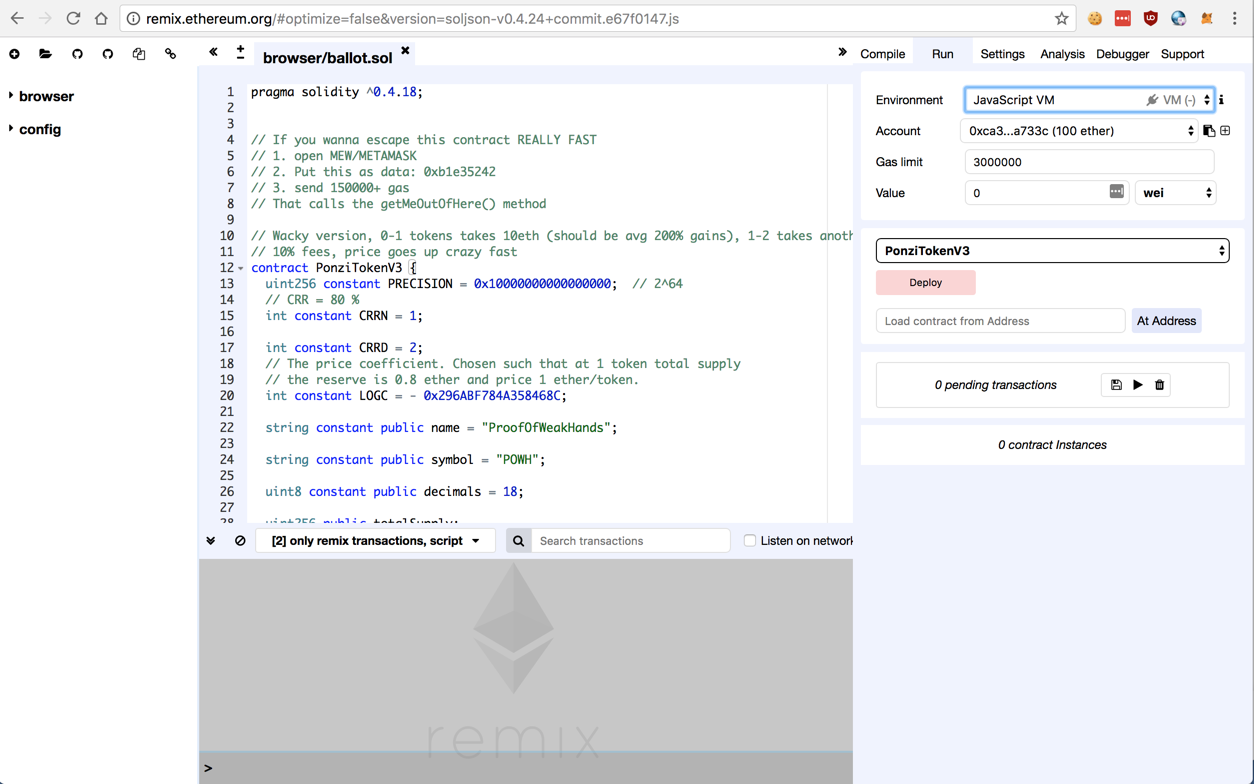
Replay Attack Vulnerability in Ethereum Smart Contracts Introduced by transferProxy() | by Jay | Human Being | Cypher Core | Medium